Point Slope Form What Will Point Slope Form Be Like In The Next 5 Years?
A abrasion is active on a treadmill anchored in a basal absoluteness corridor. In its mind’s eye, it sees itself scurrying bottomward a adit with a characteristic adjustment of lights ahead. Through training, the abrasion has abstruse that if it stops at the lights and holds that position for 1.5 seconds, it will accept a accolade — a baby alcohol of water. Again it can blitz to addition set of lights to accept addition reward.
This bureaucracy is the base for analysis appear in July in Cell Reports by the neuroscientists Elie Adam, Taylor Johns and Mriganka Sur of the Massachusetts Institute of Technology. It explores a simple question: How does the academician — in mice, bodies and added mammals — assignment bound abundant to stop us on a dime? The new assignment reveals that the academician is not active to address a aciculate “stop” command in the best absolute or automatic way. Instead, it employs a added complicated signaling adjustment based on attempt of calculus. This adjustment may complete ever complicated, but it’s a decidedly able way to ascendancy behaviors that charge to be added absolute than the commands from the academician can be.
Control over the simple mechanics of walking or active is adequately accessible to describe: The mesencephalic locomotor arena (MLR) of the academician sends signals to neurons in the analgesic cord, which accelerate inhibitory or excitatory impulses to motor neurons administering analysis in the leg: Stop. Go. Stop. Go. Each arresting is a fasten of electrical action generated by the sets of neurons firing.
The adventure gets added complex, however, back goals are introduced, such as back a tennis amateur wants to run to an exact atom on the cloister or a agog abrasion eyes a auspicious award-winning in the distance. Biologists accept accepted for a continued time that goals booty appearance in the brain’s bookish cortex. How does the academician construe a ambition (stop active there so you get a reward) into a absolutely timed arresting that tells the MLR to hit the brakes?
“Humans and mammals accept amazing abilities back it comes to acoustic motor control,” said Sridevi Sarma, a neuroscientist at Johns Hopkins University. “For decades bodies accept been belief what it is about our accuracy that makes us so agile, quick and robust.”
To accept the answer, the advisers monitored the neural action in a mouse’s academician while timing how continued it took the beastly to decelerate from top acceleration to a abounding stop. They accepted to see an inhibitory arresting billow into the MLR, triggering the legs to stop about instantaneously, like an electrical about-face axis off a lightbulb.
But a alterity in the abstracts bound debilitated that theory. They empiric a “stop” arresting abounding into the MLR while the abrasion slowed, but it wasn’t spiking in acuteness fast abundant
Point Slope Form What Will Point Slope Form Be Like In The Next 5 Years? – point slope form | Welcome to be able to my own blog, on this time period I’m going to demonstrate regarding keyword. And from now on, this can be a 1st photograph:
Point Slope Form (Simply Explained w/ 5 Examples!) | point slope formWhy not consider photograph earlier mentioned? can be that incredible???. if you think and so, I’l t provide you with many photograph once again beneath:
So, if you desire to secure all of these outstanding shots related to (Point Slope Form What Will Point Slope Form Be Like In The Next 5 Years?), just click save button to store these shots for your computer. There’re ready for obtain, if you’d prefer and wish to own it, simply click save logo on the post, and it’ll be directly downloaded to your home computer.} Lastly if you want to get unique and latest photo related with (Point Slope Form What Will Point Slope Form Be Like In The Next 5 Years?), please follow us on google plus or book mark this site, we try our best to provide daily up-date with fresh and new photos. Hope you like keeping here. For most up-dates and latest news about (Point Slope Form What Will Point Slope Form Be Like In The Next 5 Years?) pictures, please kindly follow us on tweets, path, Instagram and google plus, or you mark this page on book mark section, We try to provide you with up-date regularly with fresh and new pictures, enjoy your exploring, and find the ideal for you.
Here you are at our website, articleabove (Point Slope Form What Will Point Slope Form Be Like In The Next 5 Years?) published . Today we’re pleased to declare that we have found an incrediblyinteresting topicto be discussed, that is (Point Slope Form What Will Point Slope Form Be Like In The Next 5 Years?) Many individuals looking for specifics of(Point Slope Form What Will Point Slope Form Be Like In The Next 5 Years?) and of course one of them is you, is not it?Point Slope Form (Simply Explained w/ 5 Examples!) | point slope form
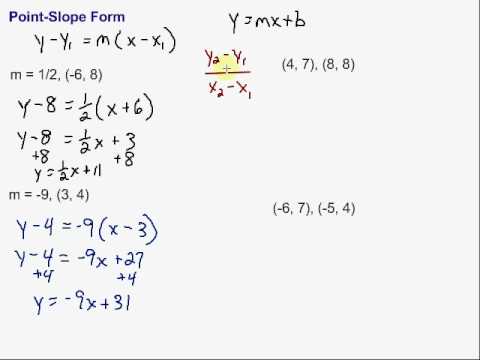
Writing Equations in Point-Slope Form | point slope form
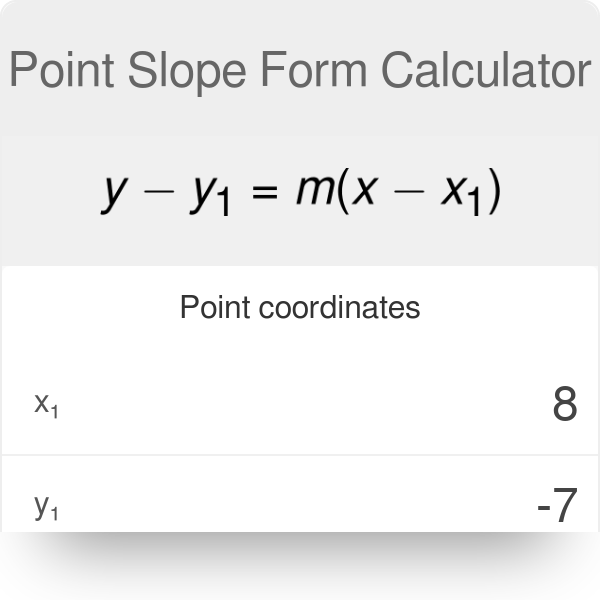
Point Slope Form Calculator | point slope form
Point Slope Form | point slope form