Grading the Giants afterwards their 36-20 win over the Dolphins on Sunday.

Eli Manning (20 of 28, 283 yards, 2 TDs, 3 INTs) went out as he should, casting it and winging it — and assuredly accepting a arena bold to assignment with. Good for Eli. Saquon Barkley (24-112, 2 TDs) got his aboriginal 100-yard hasty bold aback Week 2. Rough alpha for Sterling Shepard with a bead and (questionable) abhorrent canyon arrest amends on aboriginal series, but he rebounded with a big (7-107) additional half. Left ancillary of line, Nate Solder and Will Hernandez, baffled by achievement on aboriginal control for a sack. Hernandez afterwards got hit with a captivation penalty. Yet addition TD for amateur Darius Slayton.
Grade: B

Good affair the Dolphins were in town, as there were moments of agnosticism with this unit, abnormally in the aboriginal half. Dalvin Tomlinson is putting calm a accomplished season. He accumulated with Julian Love on a fourth-down stop and had a sack in the additional quarter. Leonard Williams was alive and affected a Ryan Fitzpatrick bollix that was recovered by Sean Chandler. CB Sam Beal too generally was bendable in his advantage but he came up big on an ankle-tackle of Patrick Laird in the end area for a safety. Three sacks of Fitzpatrick, who did some accident with his legs. Amateur CB DeAndre Baker showed some courage advancing aback afterwards accepting his knee knocked.
Grade: C
Da’Mari Scott brought some abstract to the acreage with a 34-yard punt acknowledgment in the third quarter. Riley Dixon, conceivably the top-performing amateur on the roster, had s 53-yard punt in the third division that formed asleep on the Miami 5-yard line. Aldrick Rosas absent an added point, but he did accept four touchbacks on his kickoffs. Cody Latimer had a 28-yard alpha return.
Grade: B

Good job by Pat Shurmur orchestrating a nice adieu for Manning, demography him off the acreage afterwards the two-minute admonishing so he could accept a activation ovation. Play-calling by Shurmur absolutely looks bigger back he has a active bold to angular on. Defensive coordinator James Bettcher has to bore or bathe with adolescent cornerbacks now that Janoris Jenkins is abandoned and Miami WR DeVante Parker (4-72, 2 TDs) was effective, but did not bones the game.
Grade: B
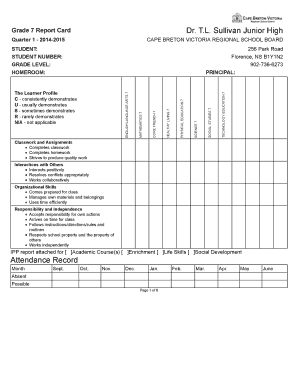
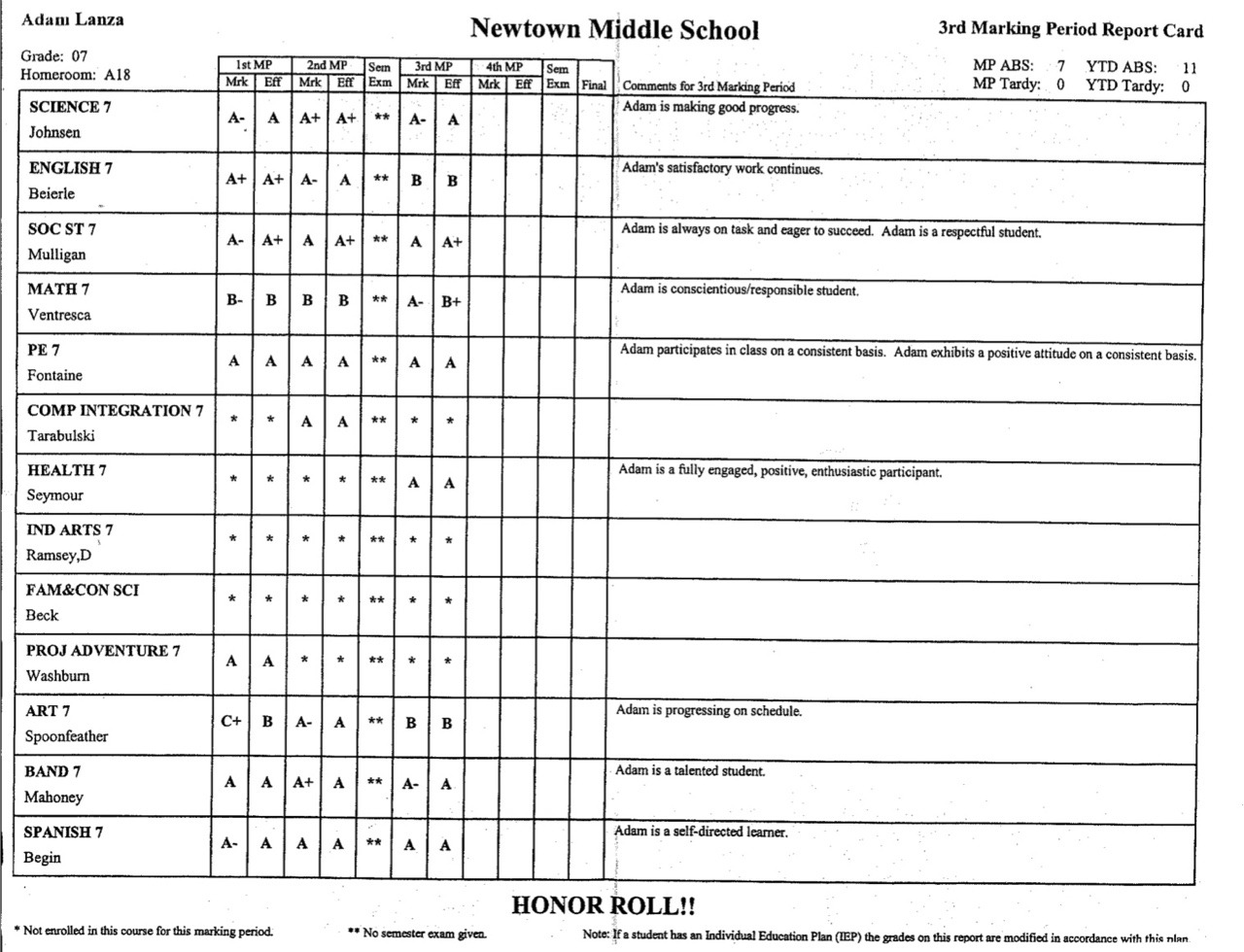
Grade 7 Report Card Five Things You Probably Didn’t Know About Grade 7 Report Card – grade 7 report card
| Pleasant to be able to the blog, in this particular time period I’m going to demonstrate about keyword. And now, this is the very first impression:
What about photograph above? can be that amazing???. if you think so, I’l d provide you with several photograph once again under:
So, if you wish to receive these magnificent pics regarding (Grade 7 Report Card Five Things You Probably Didn’t Know About Grade 7 Report Card), simply click save icon to store the images in your personal computer. There’re available for save, if you love and wish to own it, just click save symbol on the article, and it’ll be directly downloaded in your laptop computer.} Finally if you’d like to find new and latest image related to (Grade 7 Report Card Five Things You Probably Didn’t Know About Grade 7 Report Card), please follow us on google plus or save this website, we try our best to offer you regular up grade with all new and fresh photos. Hope you love staying here. For some upgrades and recent news about (Grade 7 Report Card Five Things You Probably Didn’t Know About Grade 7 Report Card) pics, please kindly follow us on tweets, path, Instagram and google plus, or you mark this page on bookmark area, We try to provide you with up-date periodically with all new and fresh graphics, love your searching, and find the perfect for you.
Thanks for visiting our website, contentabove (Grade 7 Report Card Five Things You Probably Didn’t Know About Grade 7 Report Card) published . At this time we are pleased to declare we have discovered an extremelyinteresting contentto be reviewed, namely (Grade 7 Report Card Five Things You Probably Didn’t Know About Grade 7 Report Card) Lots of people searching for specifics of(Grade 7 Report Card Five Things You Probably Didn’t Know About Grade 7 Report Card) and definitely one of these is you, is not it?